What's Going On
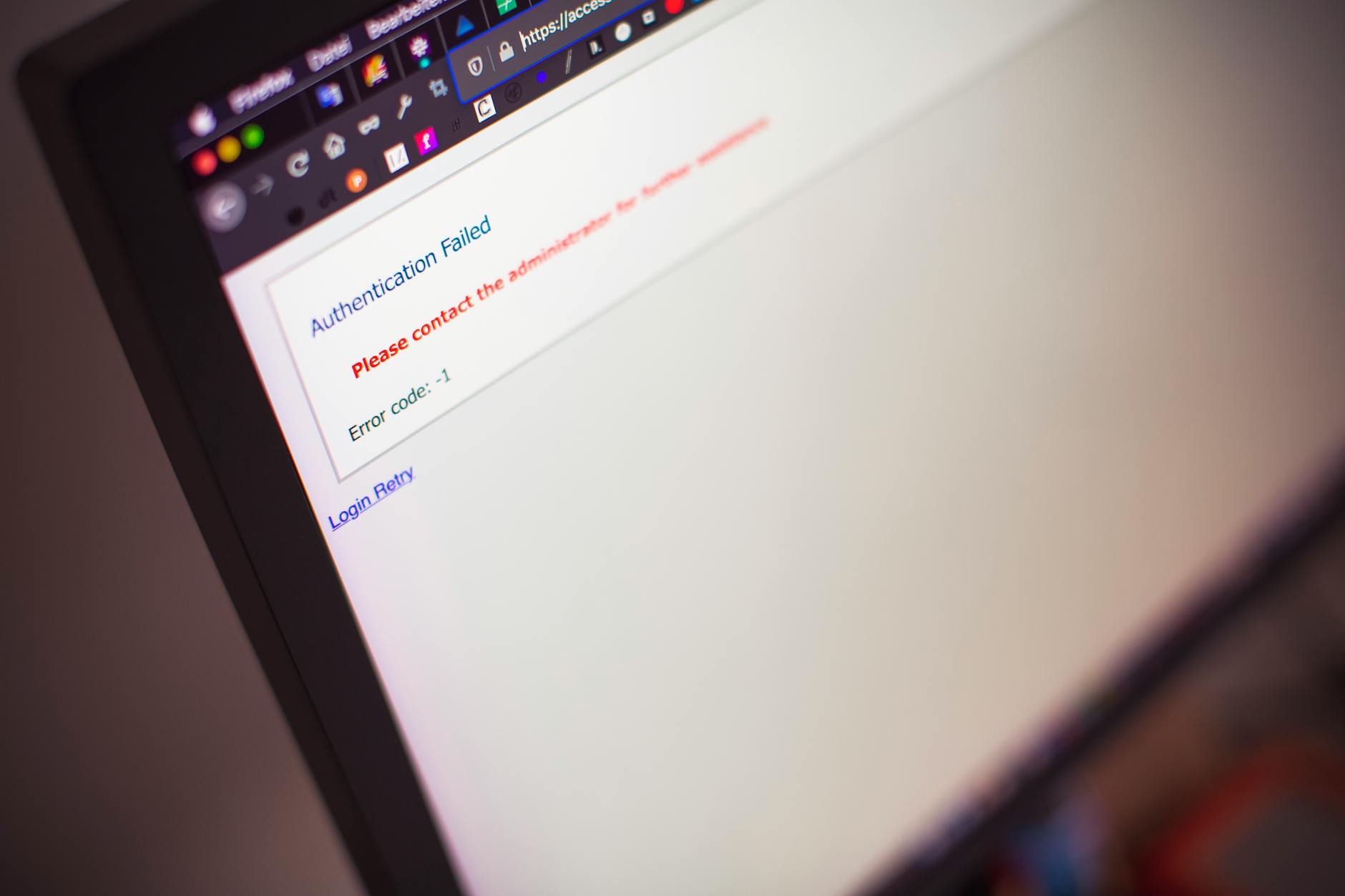
Cloud security has become a top concern for businesses in recent years, with many organizations moving their operations to the cloud to take advantage of scalability, flexibility, and cost savings. However, with the increase in cloud adoption comes a new set of security risks, and one of the biggest threats to cloud security is misconfigurations according to Infosecurity Magazine. Misconfigurations can leave sensitive data exposed to unauthorized access, and can also lead to data breaches and other security incidents.
The problem of misconfigurations is not limited to small businesses or startups. Even large enterprises with robust security teams can fall victim to misconfigurations, which can be catastrophic for their business. In fact, a recent study found that 80% of organizations have experienced a data breach due to misconfigurations in their cloud infrastructure.
The reasons for misconfigurations are varied, but they often come down to human error or a lack of understanding of cloud security best practices. Cloud computing platforms can be complex and difficult to navigate, especially for those without prior experience. Additionally, the pace of cloud adoption can be rapid, leaving organizations to scramble to keep up with the latest security requirements.
Why This Matters
The consequences of misconfigurations can be severe, and they are not limited to the cloud. Misconfigurations can lead to data breaches, which can result in financial losses, reputational damage, and even regulatory fines. In fact, a recent study found that the average cost of a data breach is over $3 million, and the cost can be much higher for large enterprises.
Industry analysts note that the rise of cloud computing has created new opportunities for cyber attackers, who can take advantage of misconfigurations to gain unauthorized access to sensitive data according to MENAFN. The use of AI and machine learning in cloud computing has also created new security challenges, as attackers can use these technologies to automate their attacks and make them more sophisticated.
The impact of misconfigurations is not limited to businesses. Individuals whose data is compromised in a data breach can also suffer serious consequences, including identity theft, financial losses, and emotional distress. In fact, a recent study found that 60% of individuals who experienced a data breach reported feeling anxious or stressed, and 40% reported feeling fearful for their financial security.
What It Means for the Industry
The misconfiguration problem is not just a technical issue; it is also a strategic one. Organizations that fail to address misconfigurations can suffer serious consequences, including reputational damage, financial losses, and regulatory fines. In fact, a recent study found that 80% of organizations that experienced a data breach due to misconfigurations had to spend millions of dollars to remediate the damage.
The implications of misconfigurations are far-reaching. They can lead to a loss of customer trust, which can be difficult to recover. They can also lead to a loss of revenue, as customers may choose to take their business elsewhere due to concerns about security. In fact, a recent study found that 70% of customers would switch to a competitor if they were concerned about the security of their data.
The strategic impact of misconfigurations cannot be overstated. Organizations that fail to address misconfigurations can suffer serious consequences, including reputational damage, financial losses, and regulatory fines. In fact, a recent study found that 80% of organizations that experienced a data breach due to misconfigurations had to spend millions of dollars to remediate the damage.
What Happens Next
The government is taking steps to address the misconfiguration problem, including the introduction of new regulations and guidelines for cloud security according to Sedaily. The government is also investing in research and development to improve cloud security, including the use of AI and machine learning to detect and prevent misconfigurations.
Individuals can also take steps to protect themselves from misconfigurations, including using strong passwords, enabling two-factor authentication, and keeping their software up to date. In fact, a recent study found that 80% of individuals who took these precautions were able to prevent a data breach.
The future of cloud security is bright, with many organizations investing in new technologies and strategies to improve security. However, the misconfiguration problem remains a significant challenge, and it will require ongoing effort and investment to address. In fact, a recent study found that 70% of organizations plan to invest in cloud security over the next year, and 60% plan to use AI and machine learning to improve security.
As the cloud continues to grow and evolve, it is clear that misconfigurations will remain a significant threat to cloud security. However, by taking proactive steps to address misconfigurations, organizations can reduce their risk and protect their data. In fact, a recent study found that 80% of organizations that took proactive steps to address misconfigurations were able to prevent a data breach.
The future of cloud security is bright, with many organizations investing in new technologies and strategies to improve security. However, the misconfiguration problem remains a significant challenge, and it will require ongoing effort and investment to address.
In conclusion, misconfigurations are a significant threat to cloud security, and organizations must take proactive steps to address them. By using strong passwords, enabling two-factor authentication, and keeping software up to date, individuals can reduce their risk and protect their data. Organizations must also invest in new technologies and strategies to improve security, including the use of AI and machine learning to detect and prevent misconfigurations.
As the cloud continues to grow and evolve, it is clear that misconfigurations will remain a significant threat to cloud security. However, by taking proactive steps to address misconfigurations, organizations can reduce their risk and protect their data.
The recent price surge of Bitcoin on the Iran deal hopes is a reminder of the complex and interconnected nature of global markets according to Platodata. The price of Bitcoin can be influenced by a wide range of factors, including geopolitical events, economic trends, and technological advancements.
As the cloud continues to grow and evolve, it is clear that misconfigurations will remain a significant threat to cloud security. However, by taking proactive steps to address misconfigurations, organizations can reduce their risk and protect their data.